Opening up new capabilities for protecting private data at rest and in motion on the IBM Z series mainframe and beyond Critical system-of-record data must…
Among all the changes that fall under the digital transformation umbrella, perhaps one of the most fundamental is the shift to the software-defined enterprise. The…
What do Anthem, British Airways, CareFirst, Experian, Home Depot, the IRS, Japan Airlines, JP Morgan Chase, NASDAQ, Sony Pictures, Staples, and the US Office of…
SAVE THE DATE! MARCH 16th 8:30 a.m. PDT | 11:30 a.m. EDT | 3:30 p.m. GMT Security is increasingly difficult, hacking is easier and easier…
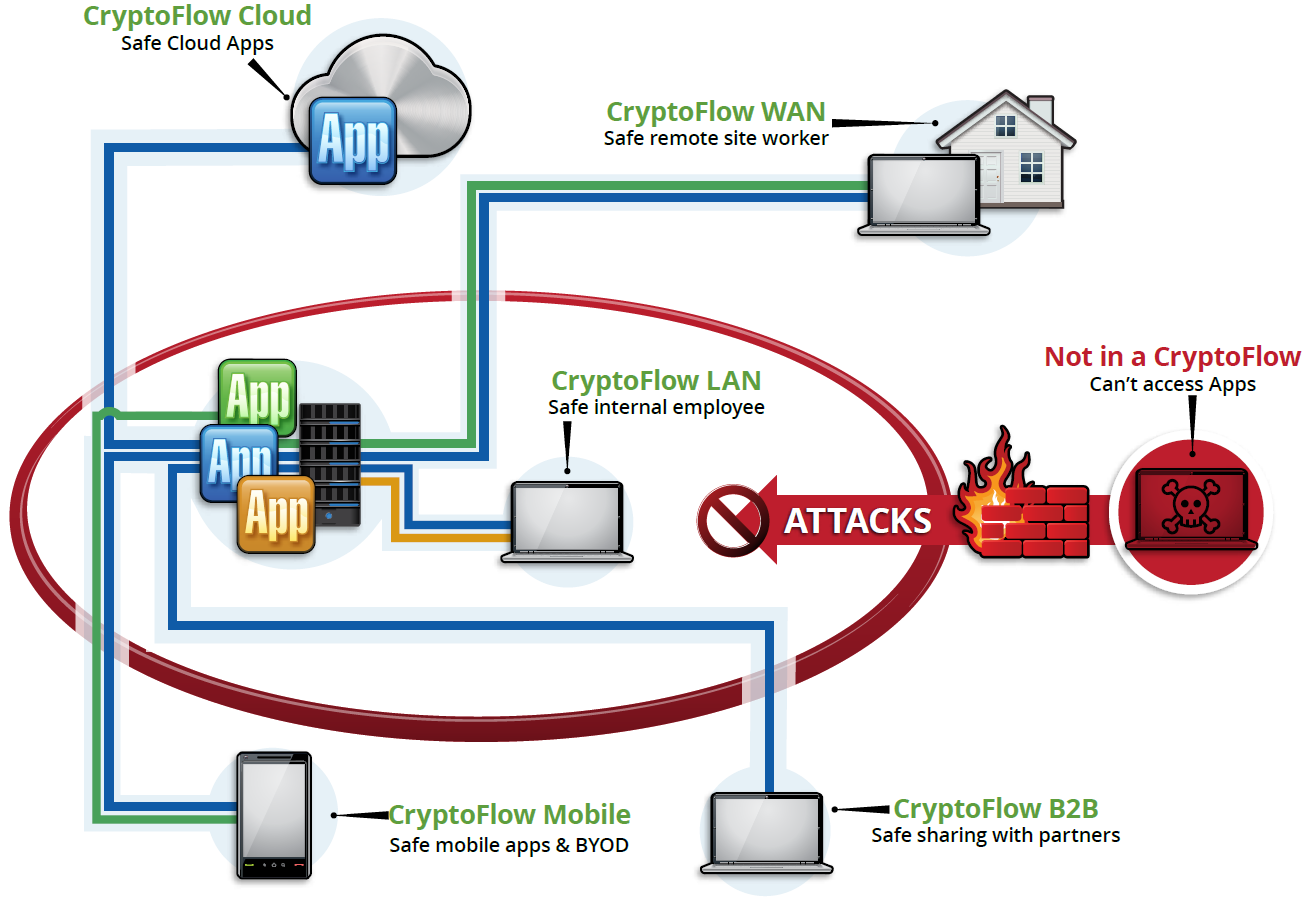
With Crypto-Segmentation, CryptoFlows automatically contain and constrain hackers exploiting compromised user credentials by blocking lateral movement from application to application. CryptoFlow solutions stop the top…
Certes CryptoFlows are the industry’s first software-defined security solution for safeguarding enterprise applications over any network for any user on any device. They enable “frictionless…
By Satyam Tyagi Snake Oil and FUD The best question is asked by Jason Bloomberg in his latest Forbes posting on the Wyndham court case,…
There are two kinds of enterprises in today’s world: the ones that know they’ve been hacked, and the ones that don’t know they’ve been hacked.…
Click here to register for this Webinar. Date and time: Thursday, September 24, 2015 8:00 am Pacific Daylight Time (San Francisco, GMT-07:00) Thursday, September…