An Intellyx Brain Candy Brief Vertex leverages its deep expertise with cyber threat intelligence (CTI) to offer an interdisciplinary intelligence platform that provides a centralized,…
brain Blog Post for next pathway by eric newcomer If the future of applications is in genAI, then the future of data for AI is…
An Intellyx Brain Candy Update Speakeasy has pivoted since we last covered the company in July 2023. Today, the company is leveraging its historic expertise…
Intellyx BrainBlog for Straiker, in The New Stack AI agents are creating new attack surfaces for enterprise security as hackers exploit MCP servers and trusted…
An Intellyx Brain Candy Brief In memory databases eliminate the latency of writing to disk and therefore are very fast, especially when returning query results.…
An Intellyx Brain Candy Update We last covered Dispersive in October 2017. Security attacks increase dramatically every year. Generative AI accelerates the pace of attack…
An Intellyx Brain Candy Brief Remember those funny high-speed data plan ads that said “we make the Internet run so fast, you’ll run out of…
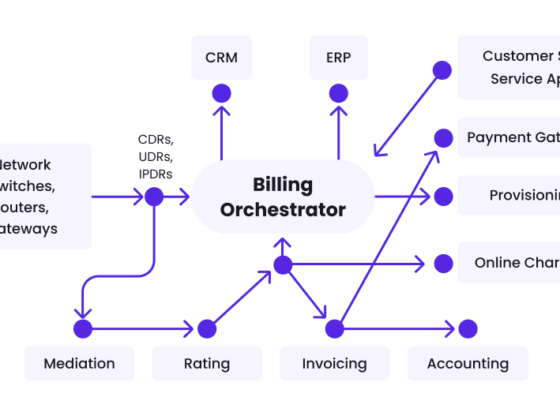
brain Blog Post for wavelo by eric newcomer Every telecom bill starts with recording an event – a phone call, text message, or stream of…
Article in The New Stack by Eric Newcomer With careful governance and validation, AI agents are increasingly gaining adoption for specific enterprise functions, according to…
Article in The New Stack by Eric Newcomer Startups in the AI world gathered at the AI Agent Conference this week in New York are scrambling to…