brain Blog Post for Next Pathway by Eric Newcomer If the future of applications is in genAI, then the future of data for AI is…
Intellyx BrainBlog for Straiker, in The New Stack AI agents are creating new attack surfaces for enterprise security as hackers exploit MCP servers and trusted…
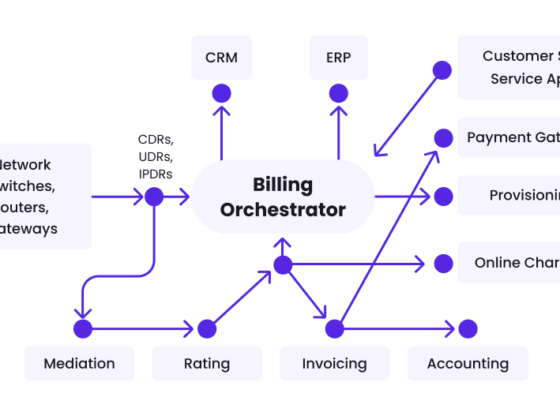
brain Blog Post for wavelo by eric newcomer Every telecom bill starts with recording an event – a phone call, text message, or stream of…
BrainBlog Post for Boomi by Eric Newcomer An old Chinese proverb says that every journey of a thousand miles starts with a single step. When…
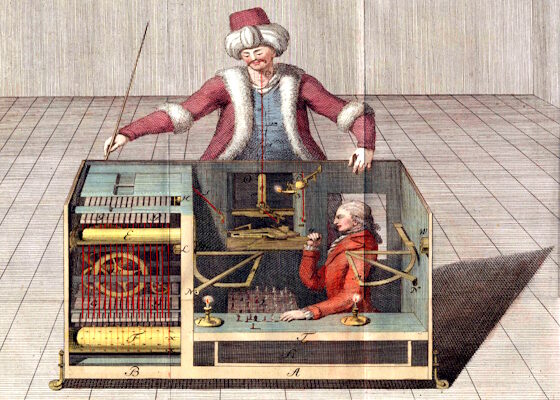
BrainBlog for Next Pathway by Jason Bloomberg In the late eighteenth century, a chess-playing automaton called the Mechanical Turk was a sensation across the courts…
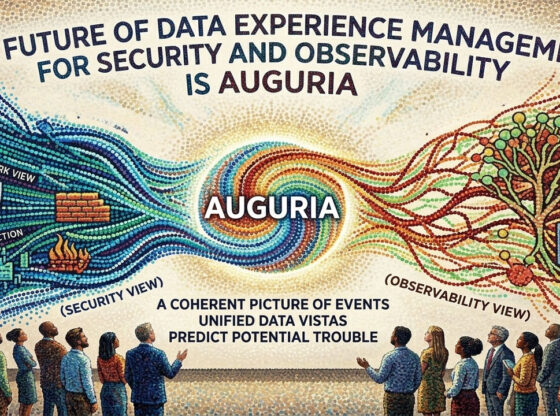
An Intellyx BrainBlog by Eric Newcomer | Part 4 of the Auguria Data Experience Series Security and observability data present different views of incidents and…
BrainBlog for Trust3 AI by Jason Bloomberg The Key to Successful AI Implementations: An independent analysis of how Trust3 AI bridges the gap between fragmented…
blog post for CROGL By Eric Newcomer How much time should you spend creating, reviewing, and maintaining playbooks for responding to security incidents? And how…
BrainBlog for Boomi by Jason Bloomberg Everyone agrees that artificial intelligence (AI) depends upon data. But as they say, the devil is in the details.…
BrainBlog for Sage AI Technologies by Jason Bloomberg Generative AI (genAI) is a legacy code modernization magic wand. Put that mainframe hairball in one end…