Last week I wrote an article on illicit cryptomining – how hackers are sneaking cryptocurrency transaction processing software onto corporate networks, personal computers, and other…
By Juan C. Perez As industry analyst Jason Bloomberg put it in a Forbes column recently, “ransomware is oh, so 2017,” as “smart hackers have turned to illicit…
An Intellyx Brain Candy Brief HeadSpin gives developers and testers the ability to experience mobile apps and sites as their users do. The company leverages…
An Intellyx Brain Candy Brief WhiteHat Security provides both dynamic and static application security testing (DAST and SAST) to help developers write more secure code,…
An Intellyx Brain Candy Brief Applitools supports testing of responsive Web apps by detecting visual differences between the appearance of a page as compared to…
An Intellyx Brain Candy Brief Insider threats may include malicious, compromised, disgruntled, or simply careless employees or other insiders. In some cases, the insider is…
By onalytica Digital transformation is the term given to the transformation of business activities, processes and models to fully leverage the opportunities of new digital technologies. The aim…
By 10tiao ITSM将把关注焦点从IT基础设施转移到以用户体验为核心的功能设计上。基于ITSM构建的应用程序将提供更丰富、更强大的用户体验,这也意味着ITSM与其他业务模块之间的数据孤岛被消除,围绕用户和业务提供全局IT管理服务。 Jason Bloomberg,Intellyx总裁 Read the entire article at http://www.10tiao.com/html/177/201803/2653203536/1.html
By Contact Center World Intellyx Talks Digital Transformation at CA’s Continuous Delivery & Agile Summit Watch the entire video at https://www.contactcenterworld.com/video.aspx?id=py57Isl6KNo&series=656c255c-22ed-40fb-822f-ca03bbb8a97e
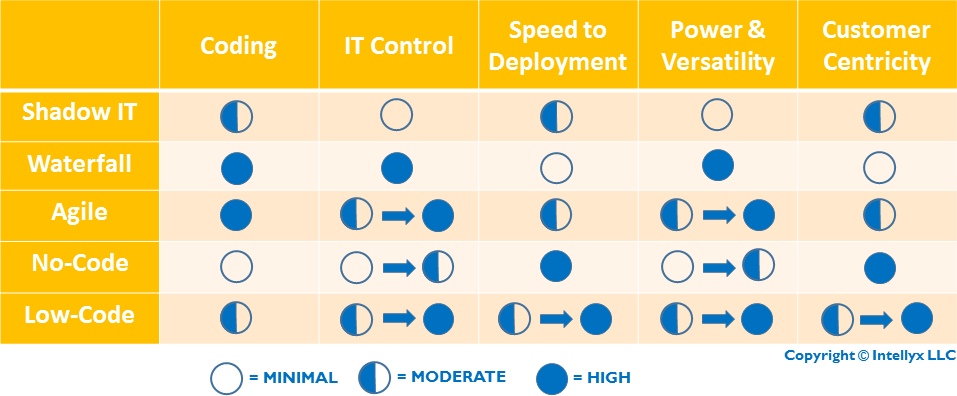
As enterprises reacted to the drawbacks of traditional, waterfall development – long timeframes, high costs, and results that rarely met customer expectations – they had…