An Intellyx Brain Candy Brief Natural Language Generation (NLG) is now a familiar part of our day-to-day experience. In enterprise scenarios, NLG typically requires extensive…
非法加密货币挖矿最阴险的方面在于,受害者对此浑然不觉。专家表示,在这种新的商业模式下,攻击者不再惩罚打开附件或运行恶意脚本的受害者,而是通过劫持系统要求支付赎金。 【51CTO.com快译】非法加密货币挖矿最阴险的方面在于,受害者对此浑然不觉。思科公司Talos威胁情报部门(简称“Talos团队”)的专家们表示,在这种新的商业模式下,攻击者不再惩罚打开附件或运行恶意脚本的受害者,而是通过劫持系统要求支付赎金。现在,攻击者在积极利用被感染系统的资源进行加密货币挖矿。 … 原文标题:Top Cyberthreat Of 2018: Illicit Cryptomining,作者:Jason Bloomberg Read the entire translation at http://netsecurity.51cto.com/art/201803/567540.htm.
Digital disruption was 2017’s “hot topic,” but in 2018 you’re behind the curve if you haven’t moved from talk to action. From the CIO to…
In most organizations, the rapid expansion of IoT deployments has happened with little strategic oversight as business leaders focused on seizing advantage. But this Wild…
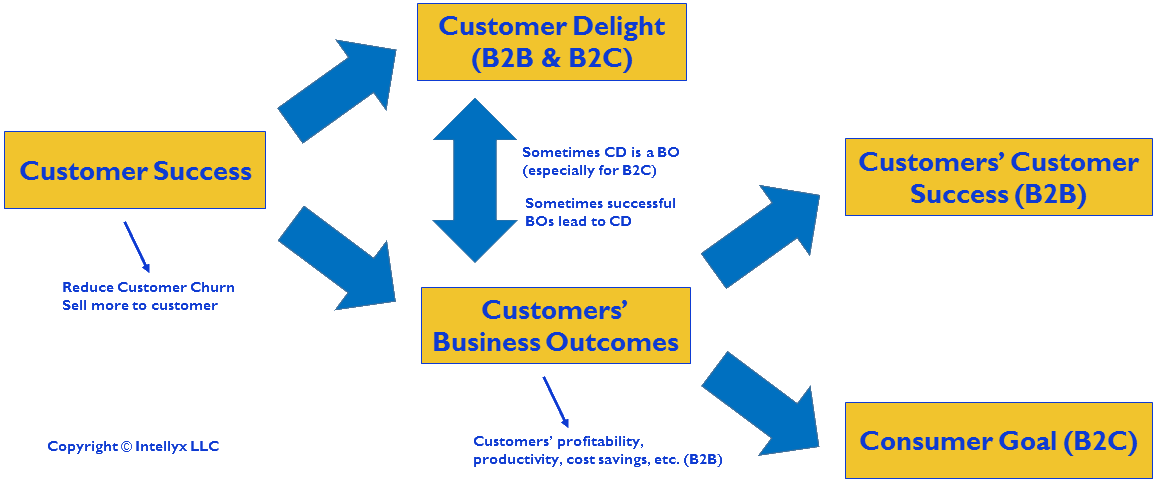
Last week, I published an article for Forbes entitled Customer Success? Pull The Other Leg. In the article, I bemoan the fact that customer success…
Ransomware is oh, so 2017. Today, all the smart hackers have turned to illicit cryptomining to fill their coffers. Due to a combination of a…
By MICHAELWYRSCH1957 „Das klingt großartig. Aber es ist einfach nicht realistisch. “ Das hat eine Gruppe von fünf leitenden IT-Führungskräften während eines Workshops, den ich vor kurzem…
An Intellyx Brain Candy Brief As software vendors get wise to popular cybersecurity attacks, they harden their offerings, pushing the attackers to come up with…
An Intellyx Brain Candy Brief Decent has yet to establish a market for the content on its Blockchain Content Distribution platform – a classic example…
As hybrid environments are becoming the de facto production state, organizations are realizing that both the operational and security challenges are growing exponentially. The question…