Last month, fellow Forbes contributor Lee Mathews reported on the recent wave of ‘Jackpotting’ attacks on ATMs in the United States. Jackpotting is where a hacker installs malware on an ATM causing it to spit out all its money.
Since legendary hacker Barnaby Jack demonstrated the ease of jackpotting at a Black Hat conference in 2010, people have been expecting such attacks to eventually hit the US.
With the US Department of Justice’s recent arrest of two men involved in this malfeasance on US soil, it’s now clear that jackpotting is a real threat here. The question remains, however: just how big?
Will hackers hit all the ATMs, or is it a simple matter to prevent further attacks? And why were ATMs still so vulnerable to this attack, eight years after jackpotting came to the attention of the ATM manufacturers as well as their customers?
And perhaps the most important question of all: what does the jackpotting trend mean for cybersecurity in general?
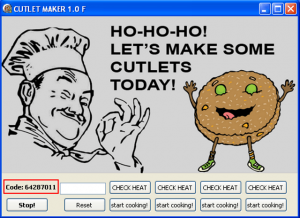
Making Cutlets
This story begins, as so many hacking stories do, on the Dark Web – hidden areas of the Internet where criminals do business.
A simple search on a malware portal turns up Cutlet Maker – the core malware package that instructs certain ATMs to spit out their dough. “Cutlet Maker requires almost no advanced knowledge or professional computer skills from the criminal,” reports Konstantin Zykov, developer and security researcher at Kaspersky Lab. “Cutlet Maker interacts with the ATM’s software and hardware, encountering almost no security obstacles at all.”
Read the entire article at https://www.forbes.com/sites/jasonbloomberg/2018/02/12/atm-jackpotting-attacks-reveal-deeper-problems/
Intellyx publishes the Agile Digital Transformation Roadmap poster, advises companies on their digital transformation initiatives, and helps vendors communicate their agility stories. As of the time of writing, Accelerite is an Intellyx customer. None of the other organizations mentioned in this article are Intellyx customers. Image credit: anonymous creator of Cutlet Maker.



