By Jason Bloomberg, published by John Wiley & Sons, 2019 “Low-Code For Dummies” is the first book of its kind, outlining the emergence of low-code…
An Intellyx Brain Candy Update Since we last covered Alluxio in September 2018, it has fine tuned its message to align with the exploding cloud-native…
An Intellyx Brain Candy Brief Most low-code vendors help their customers build applications with user-facing front ends – typically consisting of mobile and web apps.…
NetApp Inc. is a longtime leader in the enterprise storage marketplace, nudging out competitors Dell EMC, Pure Storage Inc. and Hewlett Packard Enterprise Co. for…
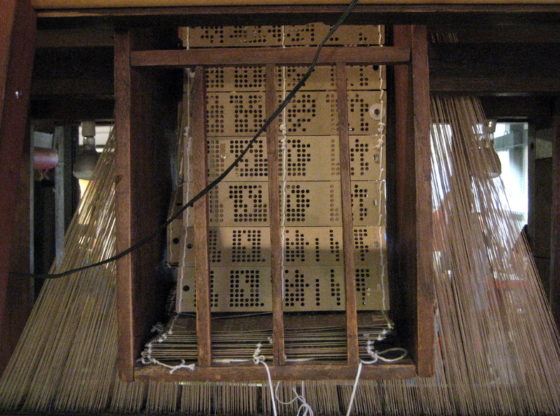
Automation has been a reality since the Jacquard loom of the early nineteenth century. And just as its punchcard technology inspired Charles Babbage and later…
An Intellyx Brain Candy Brief Rubrik is most familiar for being a vendor of backup and restore technology. While such technology is important, it’s no…
An Intellyx Brain Candy Brief There’s always been a ‘model kit’ aspect to open source software: instead of getting a finished, ready-to-deploy product, you get…
An Intellyx Brain Candy Update When we last wrote about Datical in October 2018, it offered a commercial database release management and automation tool. Today…
An Intellyx Brain Candy Update When we last wrote about XebiaLabs in December 2016, it had already established itself as a leading application release automation…
An Intellyx Brain Candy Brief Grafana Labs is the primary contributor to the Grafana and Loki open source projects, as well as one of the…