Chinese translation of an article by Jason Bloomberg 数字化转型已经风靡了五年,但直到今天,人们仍然对具体细节感到困惑。 另一方面,IT 转型更容易理解。毕竟,这显然与技术有关。它包括改变各种治理流程和改造组织孤岛,但所有这些变化都以技术为中心。 基本上,企业 IT 通常而言在很多方面都表现得很糟糕,如果我们即便只是让它变得不那么糟糕,就可以将这种改变当做胜利了。 相比之下,数字化转型以客户为中心。当然,并不是说技术对数字化转型不重要。正如我们在 Intellyx 所说,数字化转型是软件赋能(software-empowered)与客户驱动(customer-driven)的。 鉴于技术在数字化转型中发挥的重要作用,你可能会猜想数字化转型是否只是以客户为中心的 IT 转型。 然而,这两种类型的转换之间的差异要深远得多——两者之间复杂的相互关系也是如此。尝试其中一个而舍弃另一个可能是有风险的,混淆它们的风险更大。 消除差异 在 Intellyx,我们将数字化转型定义为战略性业务转型,其中客户偏好和行为推动企业技术决策。这是整个企业的端到端转型,它会影响组织的所有部分,以便将变革本身作为核心竞争力。 IT…
SiliconANGLE article by Jason English Splunk Inc. returned this week to the online format of its blockbuster annual event, Splunk .conf21, with the broad theme…
Event Retrospective from Jason English, Principal Analyst, Intellyx The concept of another big-bang software conference caused me some trepidation — after all, many well-known technology…
SiliconANGLE article by Jason Bloomberg The Cloud Native Computing Foundation’s flagship KubeCon/CloudNativeCon conference returned triumphantly to in-person mode this week in Los Angeles – albeit with the…
SiliconANGLE article by Jason Bloomberg Robotic process automation, or RPA for short, burst onto the enterprise tech landscape a handful of years ago, promising to…
SiliconANGLE article by Jason Bloomberg The cybersecurity conference Black Hat roared back to Las Vegas last week in spite of a renewed mask mandate and a virtual…
Vietnamese translation of a Cortex column by JE Xu hướng meta hiện tại của kiểm thử phần mềm ẩn – trong đó phần lớn kiểm…
SD Times Article by Jason English The current meta-trend of hidden software testing — in which much of software testing gets pushed to shift-right, post-production validation —…
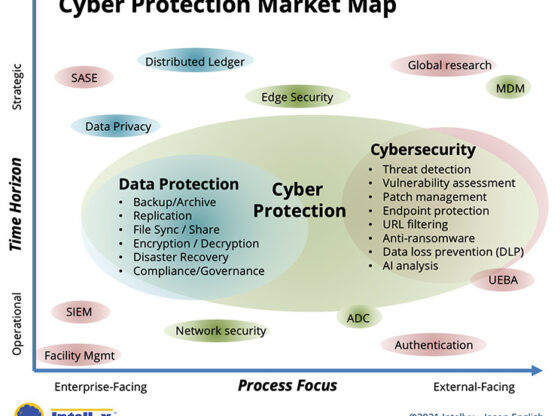
DZone Article by Jason English What Is Cyber Protection? Cyber Protection is an IT industry solution category that merges the existing spaces of data protection and…
Article by Jason English, for Tricentis Anyone involved in software delivery will tell you that automation – wherever possible – is an inherently good thing.…